It’s an era of cryptographic money, where advanced resources are put away and moved across decentralized networks, guaranteeing secure admittance to assets and delicate data is principal. Biometric validation, including Face ID check verification, has arisen as a promising answer for improving security and client experience. In any case, the ascent of biometric caricaturing strategies presents novel difficulties and dangers that should be addressed to keep up with the trustworthiness of digital money stages. In this article, we dive into the complexities of biometric confirmation taking a chance in digital money, and propose an all-encompassing way to deal with moderate these dangers.
The Promise and Peril of Biometric Authentication
Biometric authentication, utilizing remarkable actual characteristics like fingerprints or facial elements, offers a helpful and secure method for checking personality. With regards to digital currency, biometric verification improves security by decreasing dependence on conventional validation techniques powerless to phishing assaults or secret word breaks. Face ID check, specifically, has built up momentum for its consistent client experience and vigorous security highlights.
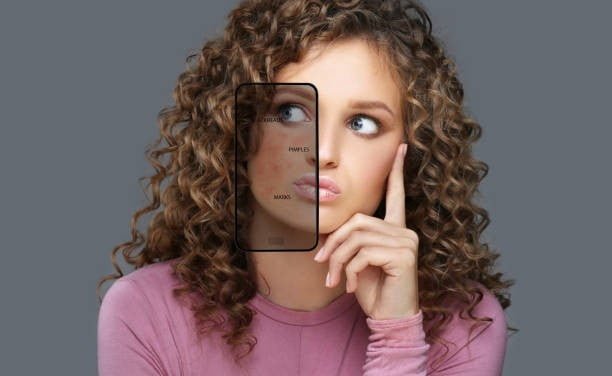
Be that as it may, the reception of biometric confirmation in digital currency presents new dangers, boss among them being biometric parodying. Biometric parodying strategies, including the utilization of high-goal photos or modern covers, can bamboozle biometric verification frameworks and award unapproved admittance to clients’ assets or delicate data. As digital money stages progressively depend on biometric validation, addressing these dangers becomes basic to protect client resources and keep up with trust in the biological system.
Understanding Biometric Spoofing Techniques
Biometric spoofing, otherwise called show assaults, takes advantage of weaknesses in biometric confirmation frameworks to sidestep safety efforts. On account of Face ID check verification, assailants might endeavor to deceive the framework by introducing an imitation or reproduction of the genuine client’s face, consequently acquiring unapproved admittance to cryptographic money wallets or records.
Different methods can be utilized to complete biometric satirizing assaults, including:
- High-Resolution Photographs: Aggressors might utilize top-notch photos or pictures of the authentic client’s face to trick facial acknowledgment frameworks.
- 3D Masks or Sculptures: Refined veils or figures made to look like the client’s face can sidestep facial acknowledgment frameworks by imitating facial highlights and forms.
- Deepfake Technology: Advances in deepfake technology empower the making of profoundly reasonable phony recordings or pictures, further muddling the discovery and counteraction of biometric mocking assaults.
Mitigating Biometric Authentication Risks
To moderate the dangers related to biometric authentication in cryptographic money, a diverse methodology is required. Here are key methodologies to address biometric spoofing and upgrade the security of cryptographic money stages:
- Biometric Liveness Recognition: Carry out biometric liveness discovery components to separate between live faces and caricature biometric information. By expecting clients to perform explicit activities during the confirmation cycle, for example, squinting or grinning, stages can check the presence of a genuine individual.
- Multifaceted Authentication (MFA): Supplement biometric confirmation with extra factors, like passwords or equipment tokens, to make a diverse security approach. MFA adds a layer of security against unapproved access, regardless of whether biometric information is compromised.
- Consistent Monitoring and Analysis: Utilize progressed irregularity location calculations to screen client conduct and verification designs for indications of dubious action or biometric satirizing endeavors. Constant examination empowers brief recognition and reaction to arising dangers.
- User Education and Awareness: Teach clients about the dangers of biometric satirizing and the significance of safely putting away and safeguarding their biometric information. Urge clients to empower security elements, for example, biometric liveness identification, and stay careful against phishing endeavors or social designing assaults.
- Normal Security Reviews and Testing: Direct customary security reviews and entrance testing to distinguish weaknesses in biometric verification frameworks and address possible shortcomings. Proactive appraisal and remediation assist with reinforcing guards against biometric mocking assaults.
Wrapping Up!
Biometric authentication holds an extraordinary commitment to upgrading security and client experience in digital money stages. Nonetheless, the dangers presented by biometric satirizing strategies highlight the significance of carrying out vigorous safety efforts and embracing a proactive way to deal with risk relief. By utilizing biometric liveness identification, multifaceted validation, consistent observing, client schooling, and ordinary security reviews, cryptographic money stages can explore the difficulties of biometric verification gambles really and defend client resources in an undeniably advanced and decentralized biological system.